Setting up a G WiFi Network for Role-Based Access Control: A Comprehensive Guide
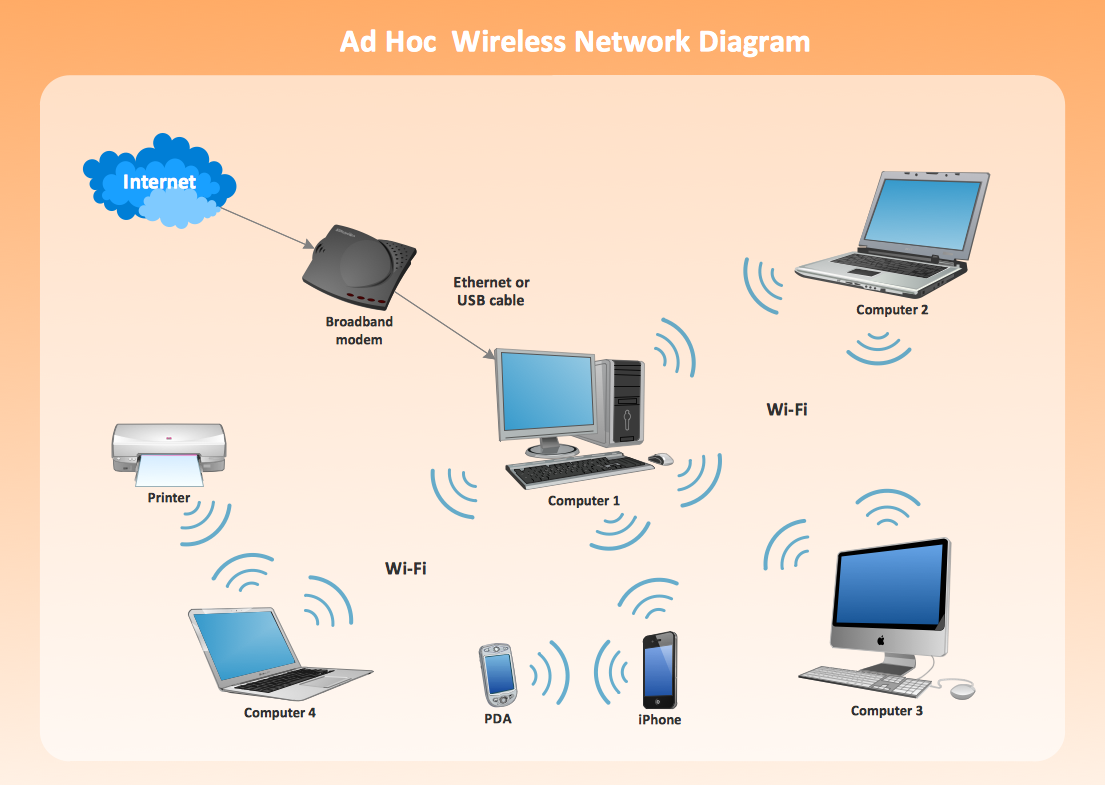
With the increasing number of devices connected to the Internet of Things (IoT), wireless networks have become an essential part of our daily lives. However, securing these networks has become a significant challenge. One way to address this issue is by implementing Role-Based Access Control (RBAC) in your wireless network. In this article, we will discuss how to set up a G WiFi network for role-based access control and explore the benefits it offers.
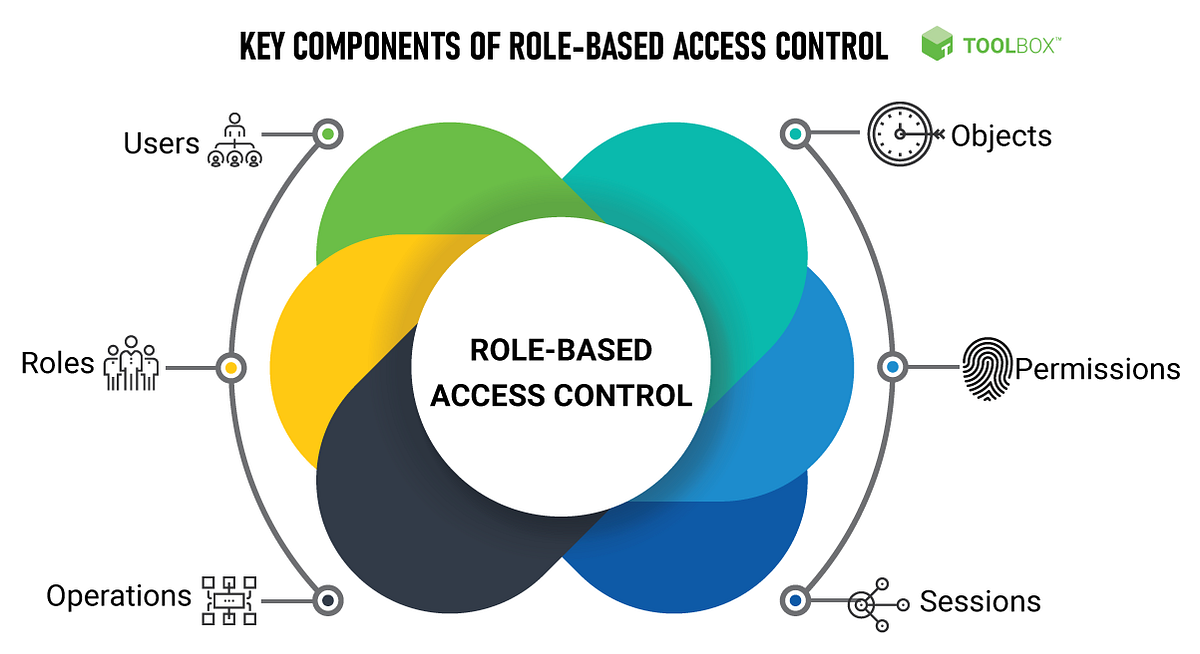
What is Role-Based Access Control (RBAC)?
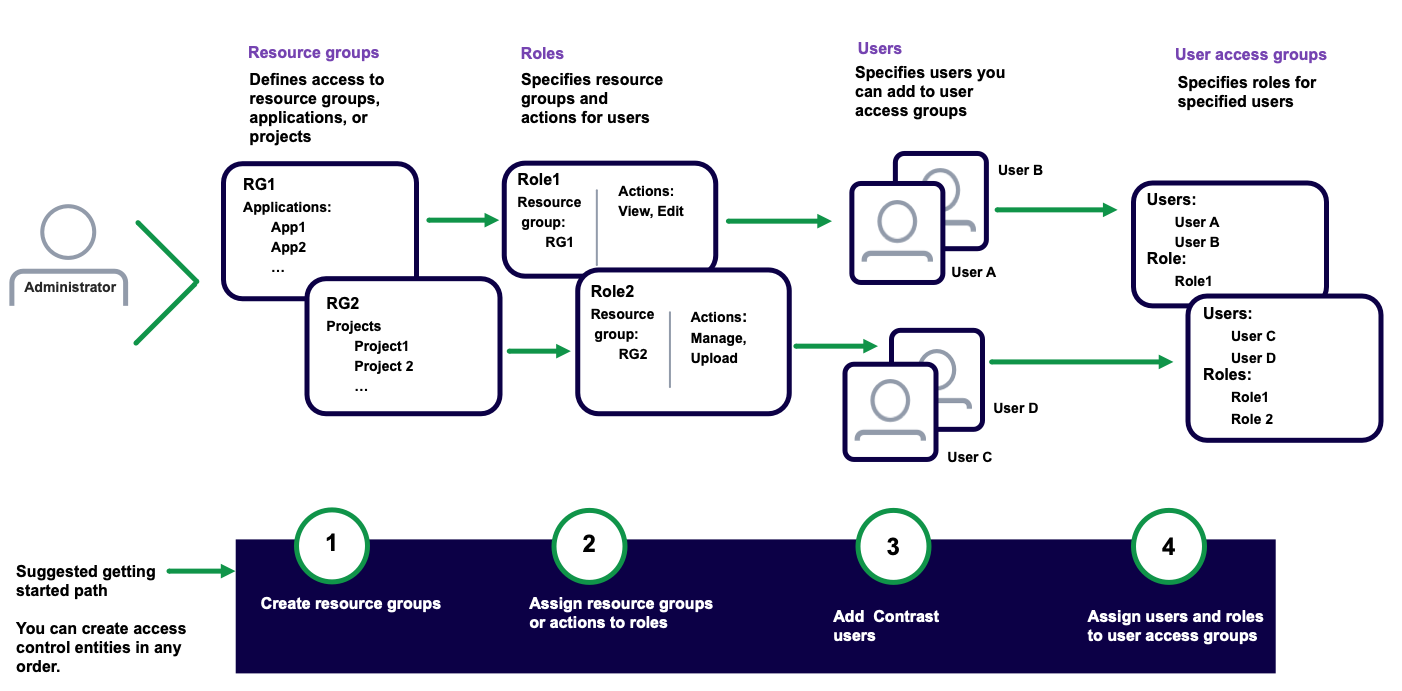
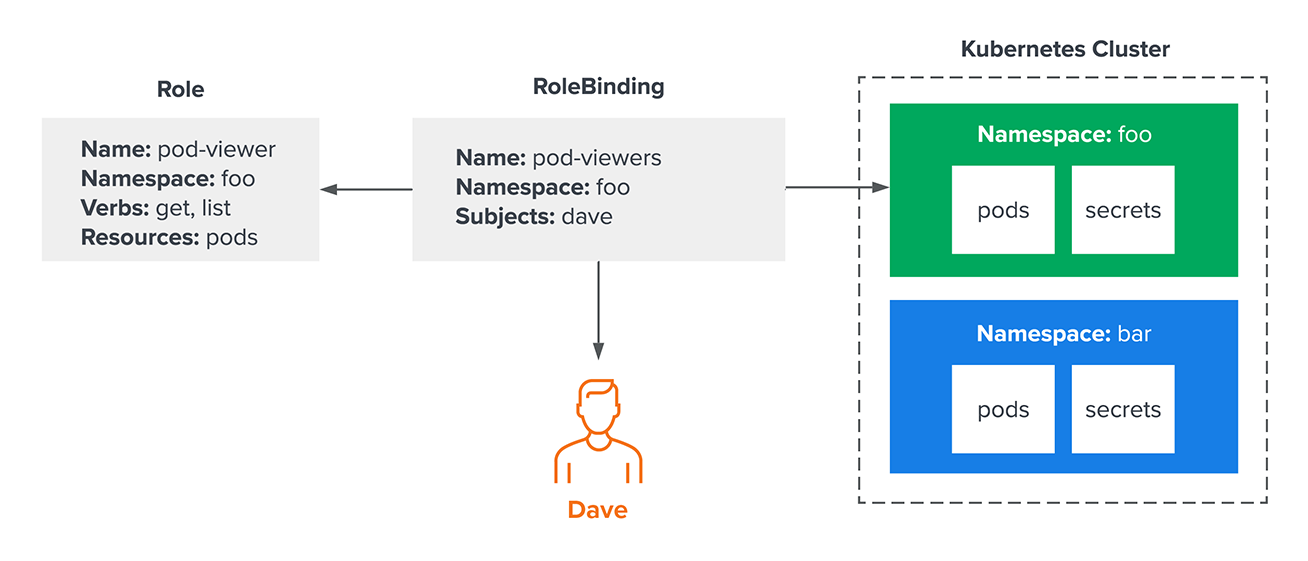
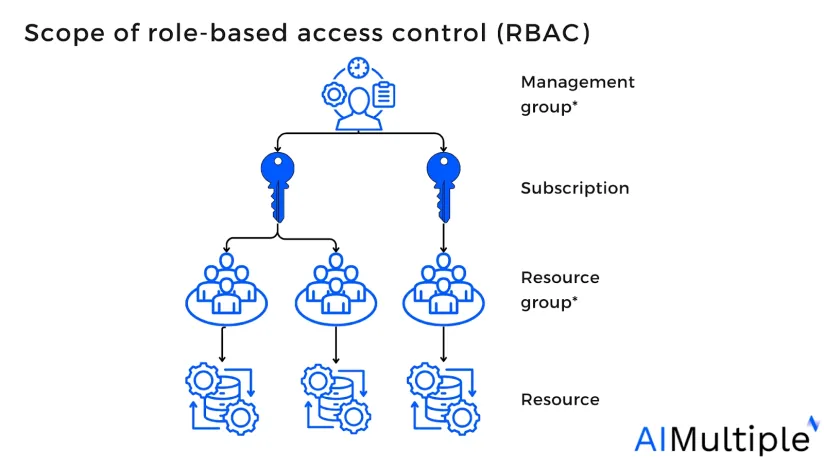
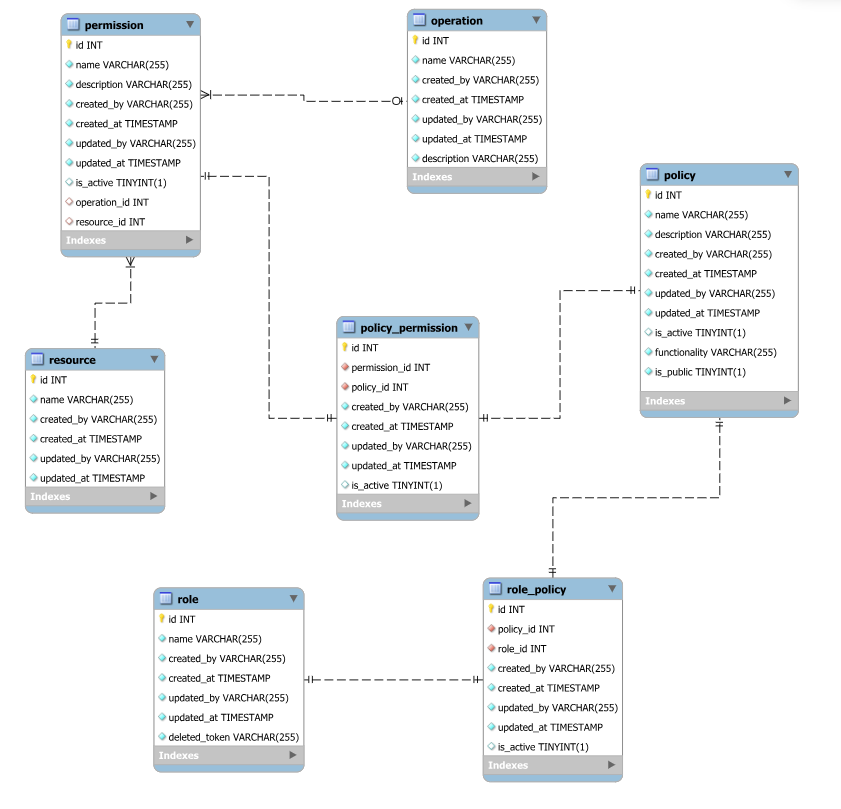
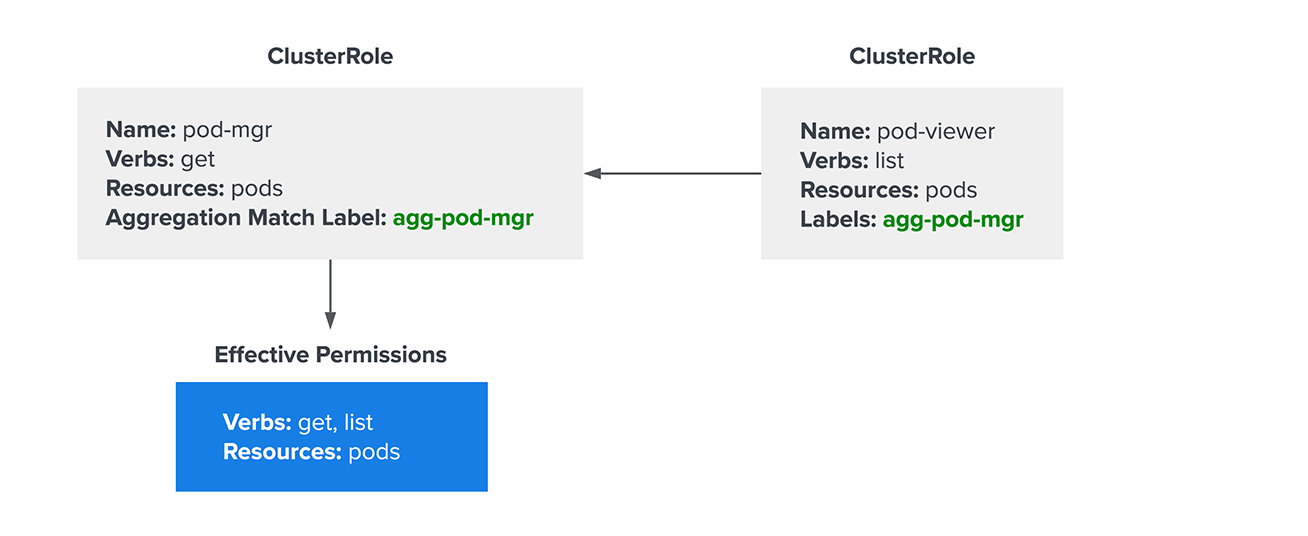
Role-Based Access Control (RBAC) is a security model that authorizes end-user access to systems, applications, and data based on predefined roles. It allows organizations to specify who has access to what resources, and at what level of access. For example, a security analyst can configure a firewall but cannot view customer data, while a sales representative can access customer accounts but not the firewall settings.
Benefits of RBAC in Wireless Networks
Implementing RBAC in your wireless network offers several benefits, including:
- Improved security: RBAC ensures that only authorized users have access to sensitive data and resources.
- Streamlined management: RBAC reduces the administrative overhead associated with managing user access.
- Compliance: RBAC helps organizations achieve regulatory compliance by restricting access to authorized personnel.
Steps to Set up a G WiFi Network for Role-Based Access Control
To set up a G WiFi network for role-based access control, follow these steps:
- Step 1: Identify Network Access Requirements and Security Policies: Determine the roles and permissions required for each user or group based on their job function, department, or level of access.
- Step 2: Configure Access Control Settings on the Wireless Access Points or Controllers: Set up RBAC settings on your wireless access points or controllers to restrict access based on user roles.
- Step 3: Authenticate Users and Devices Before Granting Network Access: Implement authentication mechanisms, such as username and password, multi-factor authentication, or RADIUS, to ensure that only authorized users gain access to the network.
- Step 4: Monitor and Audit Network Access: Regularly monitor and audit network access to ensure that only authorized users have access to sensitive data and resources.
Implementing RBAC in Cloud Resources
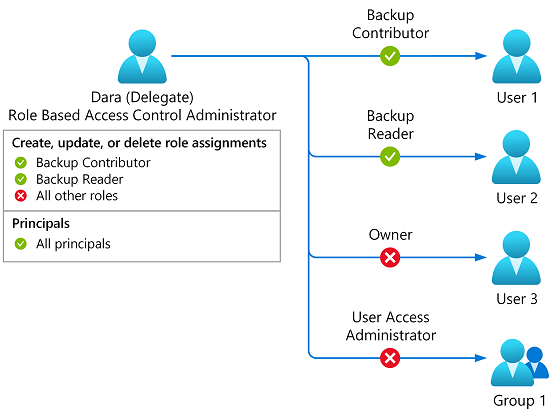
RBCA can also be implemented in cloud resources, such as Amazon Web Services (AWS), Microsoft Azure, or Google Cloud Platform (GCP). This involves setting up RBAC policies to restrict access to authorized users based on their roles and permissions.
Best Practices for Implementing RBAC in Wireless Networks
To ensure the successful implementation of RBAC in your wireless network, follow these best practices:
- Use a Robust Authentication Mechanism: Implement a secure authentication mechanism, such as multi-factor authentication, to ensure that only authorized users gain access to the network.
- Regularly Review and Update RBAC Policies: Regularly review and update RBAC policies to ensure that they remain relevant and effective.
- Monitor and Audit Network Access: Regularly monitor and audit network access to ensure that only authorized users have access to sensitive data and resources.
Conclusion
Setting up a G WiFi network for role-based access control offers several benefits, including improved security, streamlined management, and compliance with regulatory requirements. By following the steps outlined in this article and implementing RBAC best practices, you can ensure that your wireless network is secure, efficient, and compliant with regulatory requirements.
References
For more information on role-based access control, wireless networks, and cloud resources, refer to the following resources:
- IEEE 802.11 Wireless Local Area Network (WLAN) Standards
- Cloud Security Alliance (CSA) Role-Based Access Control (RBAC) Guidelines
- Microsoft Azure Role-Based Access Control (RBAC) Overview