Understanding Wireless G Network Setup for Conditional Access
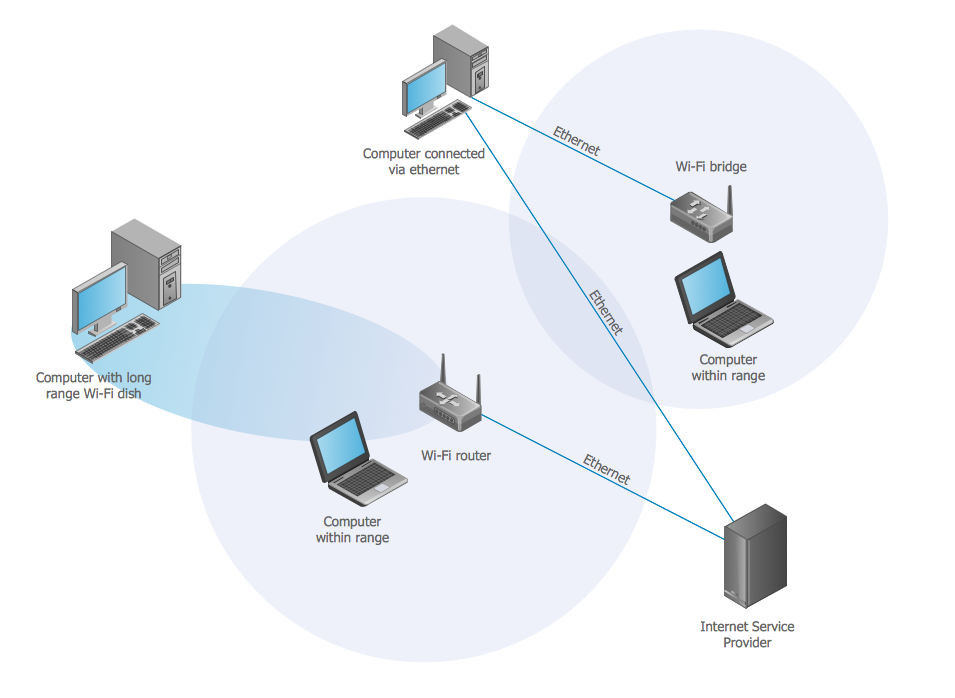
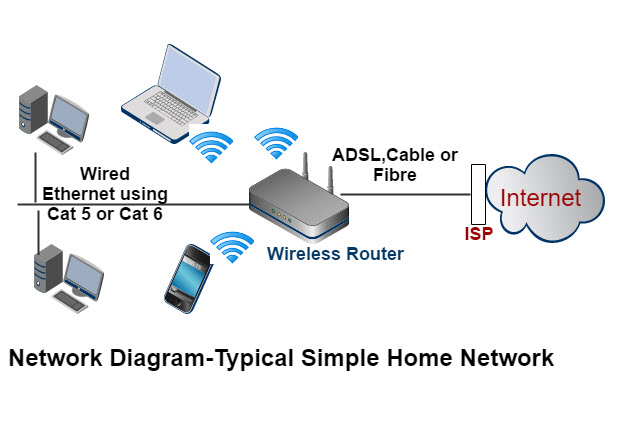
Wireless networks have become an integral part of our daily lives, providing us with convenient and easy-to-install connectivity solutions. However, this convenience comes with its own set of challenges, particularly when it comes to security. With wireless networks operating on radio waves, they can be more vulnerable to intruders than traditional wired networks. In this article, we will explore the concept of Conditional Access (CA) and how it can be achieved through a strong Wireless G network setup.
What is Conditional Access?
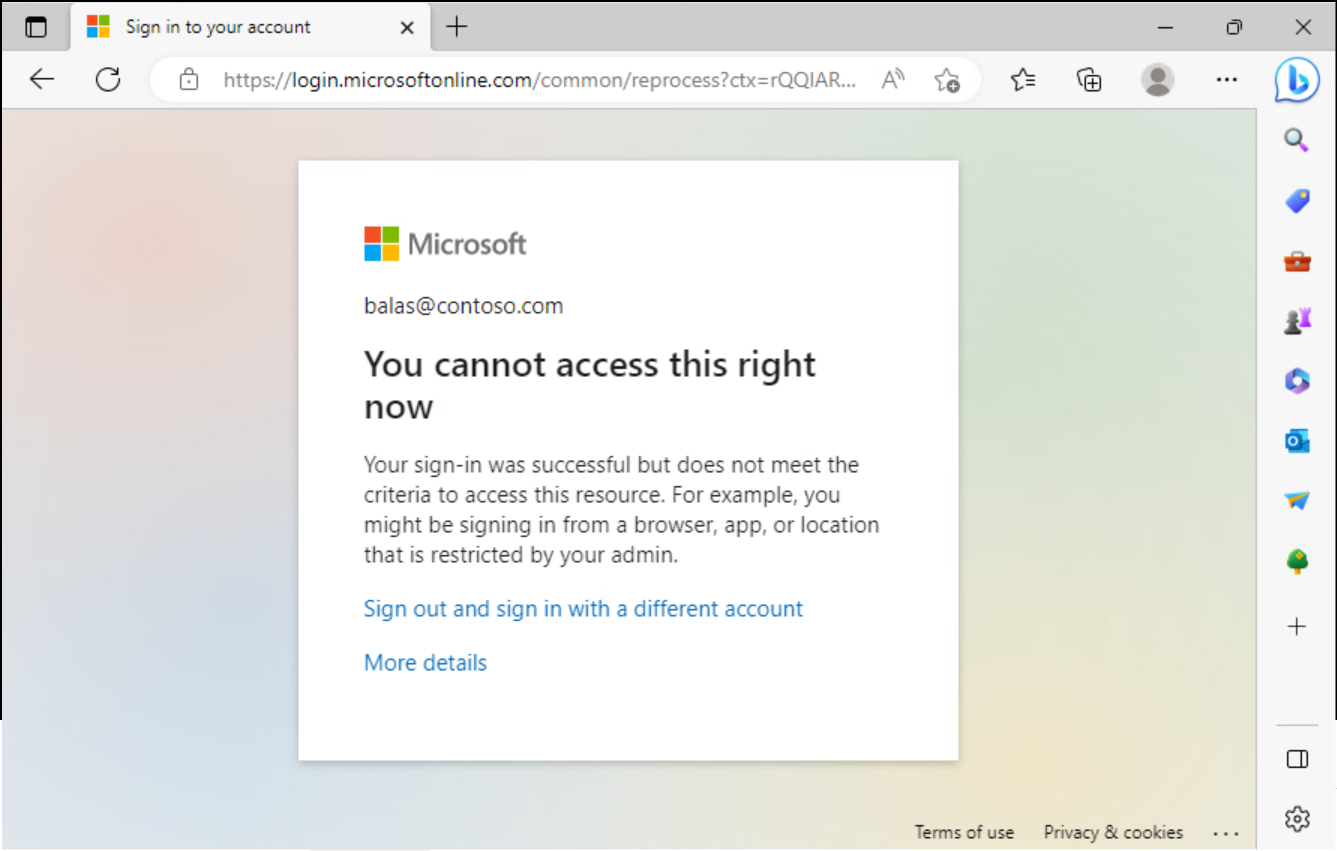
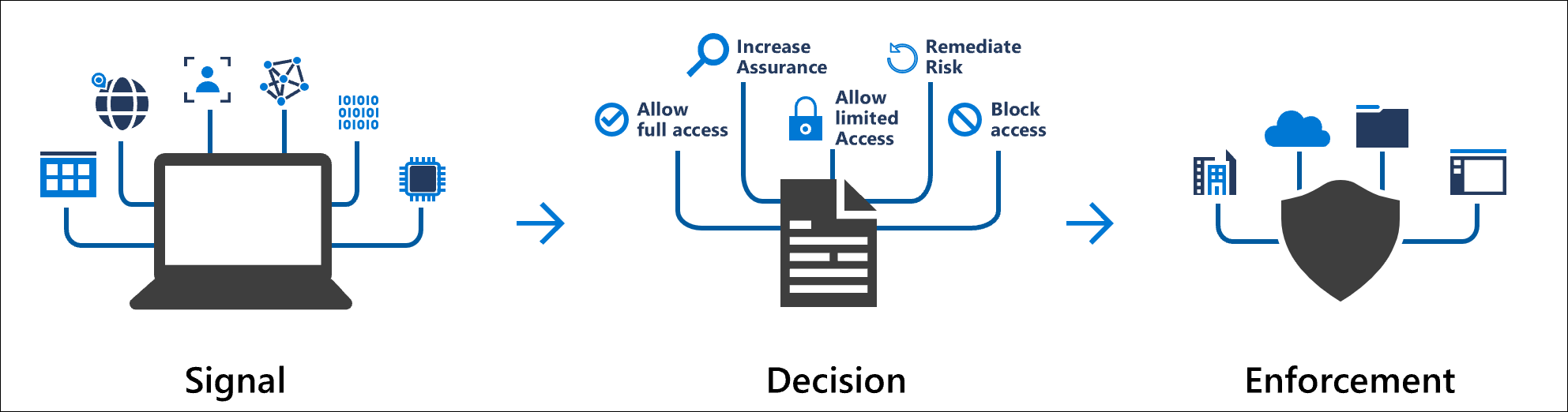
Conditional Access is a security framework that allows organizations to control which devices, users, and user groups have access to certain resources, services, and applications within an organization. This control is achieved through policies that are enforced based on specific conditions, such as user identity, device health, location, and multi-factor authentication. In essence, Conditional Access is an if-then statement for access control, ensuring that users are granted access to resources only when they meet certain criteria.
Benefits of Wireless G Network Setup for Conditional Access
A wired network setup provides several benefits, including:
- Improved security: Wired networks are less susceptible to hacking and eavesdropping compared to wireless networks.
- Reduced interference: Wired networks are less prone to interference from other devices, eliminating dropped connections and data loss.
- Increased bandwidth: Wired networks can offer faster data transfer rates compared to wireless networks.
Configuring Wireless G Network Setup for Conditional Access
To configure a wireless G network setup for Conditional Access, follow these steps:
Step 1: Set Up a Wireless Network Controller
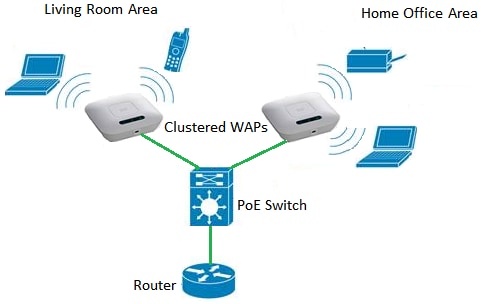
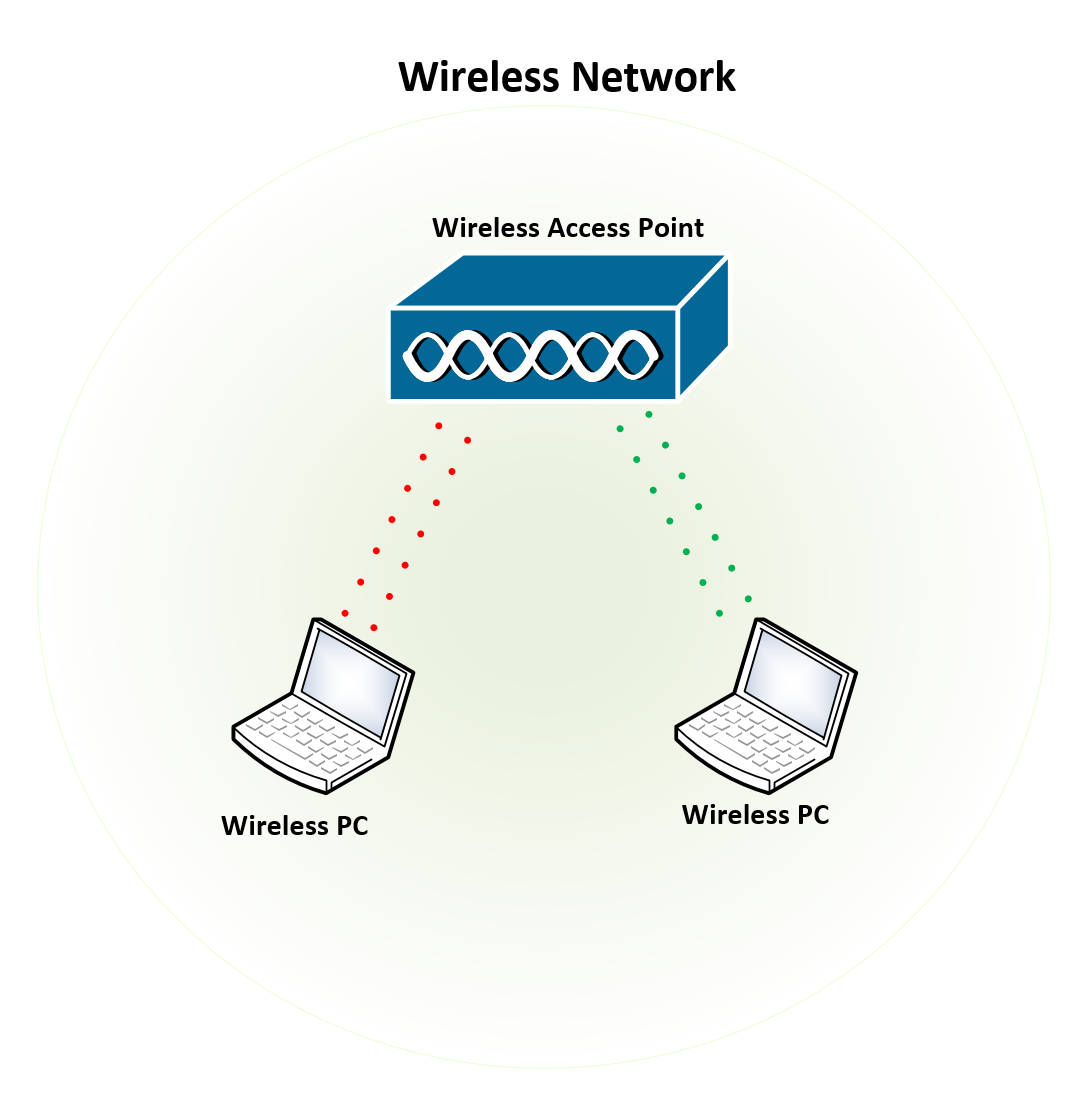
Set up a central wireless network controller to manage and configure the entire network. This controller should be able to detect and authorize devices that attempt to connect to the network.
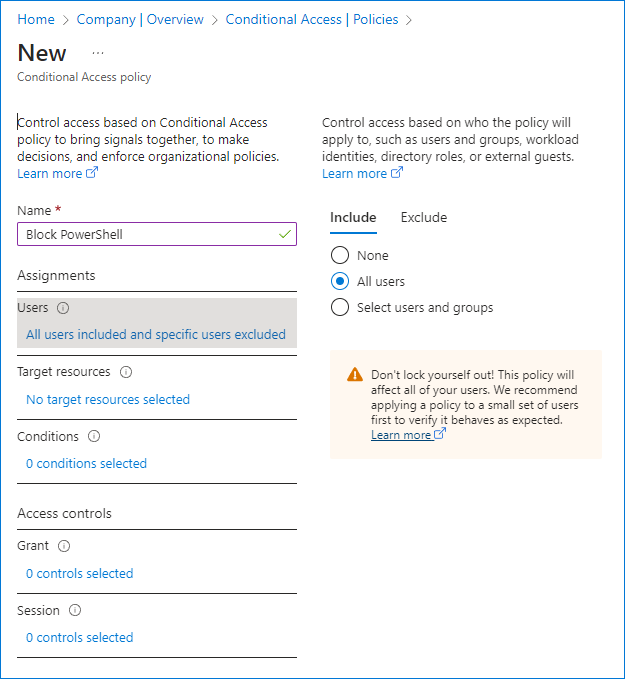
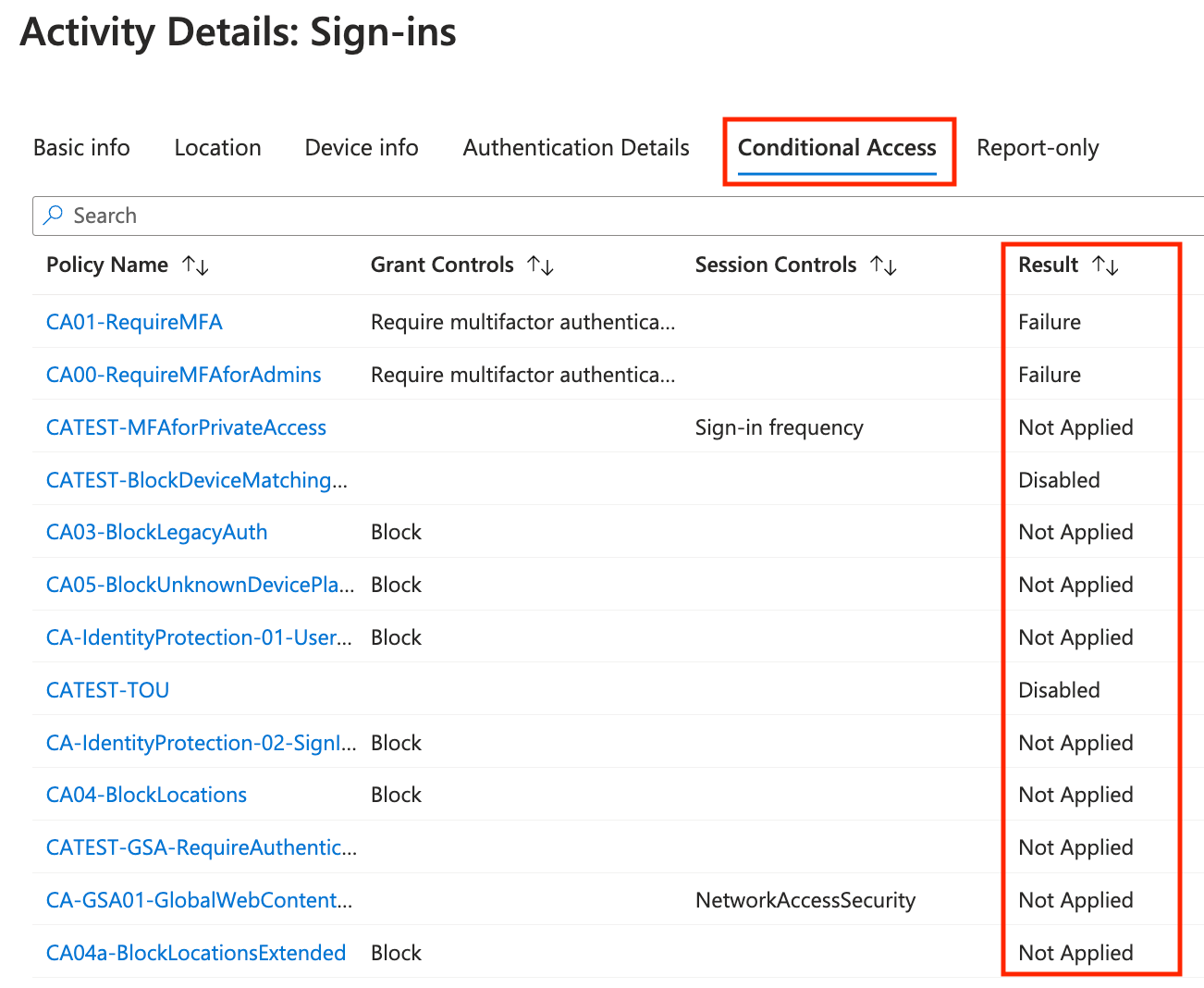
Step 2: Configure Conditional Access Policies
Configure policies that dictate which users, devices, and locations are allowed to access specific resources, services, and applications within the organization. This is achieved by creating Conditional Access policies in your Azure portal.
Step 3: Define Network-based Signals
Configure network-based signals, including trusted locations, IP ranges, and GPS-based settings, to help determine which users have access to specific resources. This enables flexible and context-aware access control.
Step 4: Integrate with Microsoft 365 and Cloud Apps
Integrate Conditional Access policies with Microsoft 365 and cloud apps to require multi-factor authentication and device compliance for accessing these resources.
Example of Conditional Access Policy
For example, let's say you set up a Conditional Access policy that requires all users attempting to access a specific application to use a fully administered device or a compliant iOS or Android device. Users who do not meet this criteria are not granted access to the application.
Security Benefits of Wireless G Network Setup for Conditional Access
A well-configured Wireless G network setup with Conditional Access provides several security benefits, including:
- Granular control over access to resources and services.
- Data encryption for sensitive information.
- Multi-factor authentication for added security.
- Intelligent threat detection and response.
Conclusion
In conclusion, a Wireless G network setup is a crucial component of any secure network infrastructure. By configuring Conditional Access policies, integrating with Microsoft 365 and cloud apps, and defining network-based signals, organizations can control who, what, and how users access their resources, services, and applications. This robust security framework ensures that sensitive information remains protected while allowing authorized users to access the resources they need to perform their jobs effectively.

![Conditional Access Policies in Azure AD: Complete Setup Guide [2026] Conditional Access Policies in Azure AD: Complete Setup Guide [2026]](https://ourcloudnetwork.com/wp-content/uploads/2022/10/Authentication-strength-in-conditional-access.png)