Optimizing G Wireless Network for Cybersecurity Measures
The Importance of Cybersecurity in Wireless Networks
As the world becomes increasingly dependent on wireless technology, the importance of cybersecurity measures has become more pronounced. Wireless networks are a key part of modern life, providing us with connectivity to the internet and enabling us to access a vast amount of information on our mobile devices. However, this increased connectivity comes with a heightened risk of cyber threats.
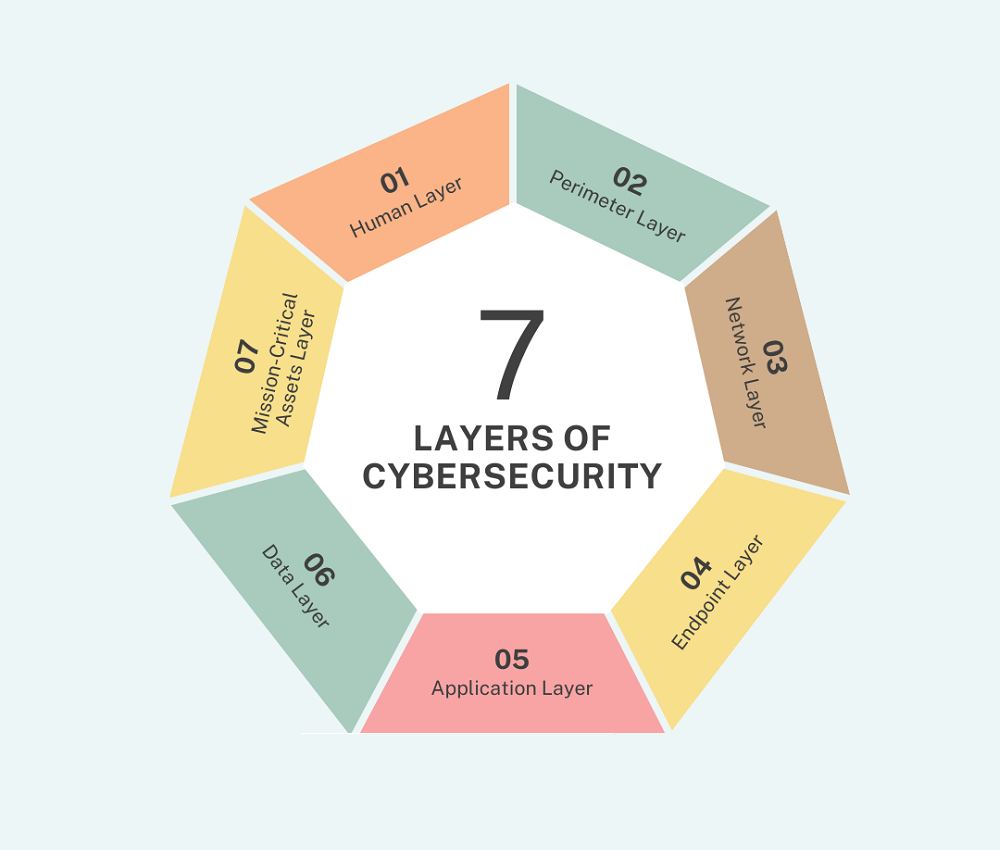
Cybersecurity Challenges in Wireless Networks
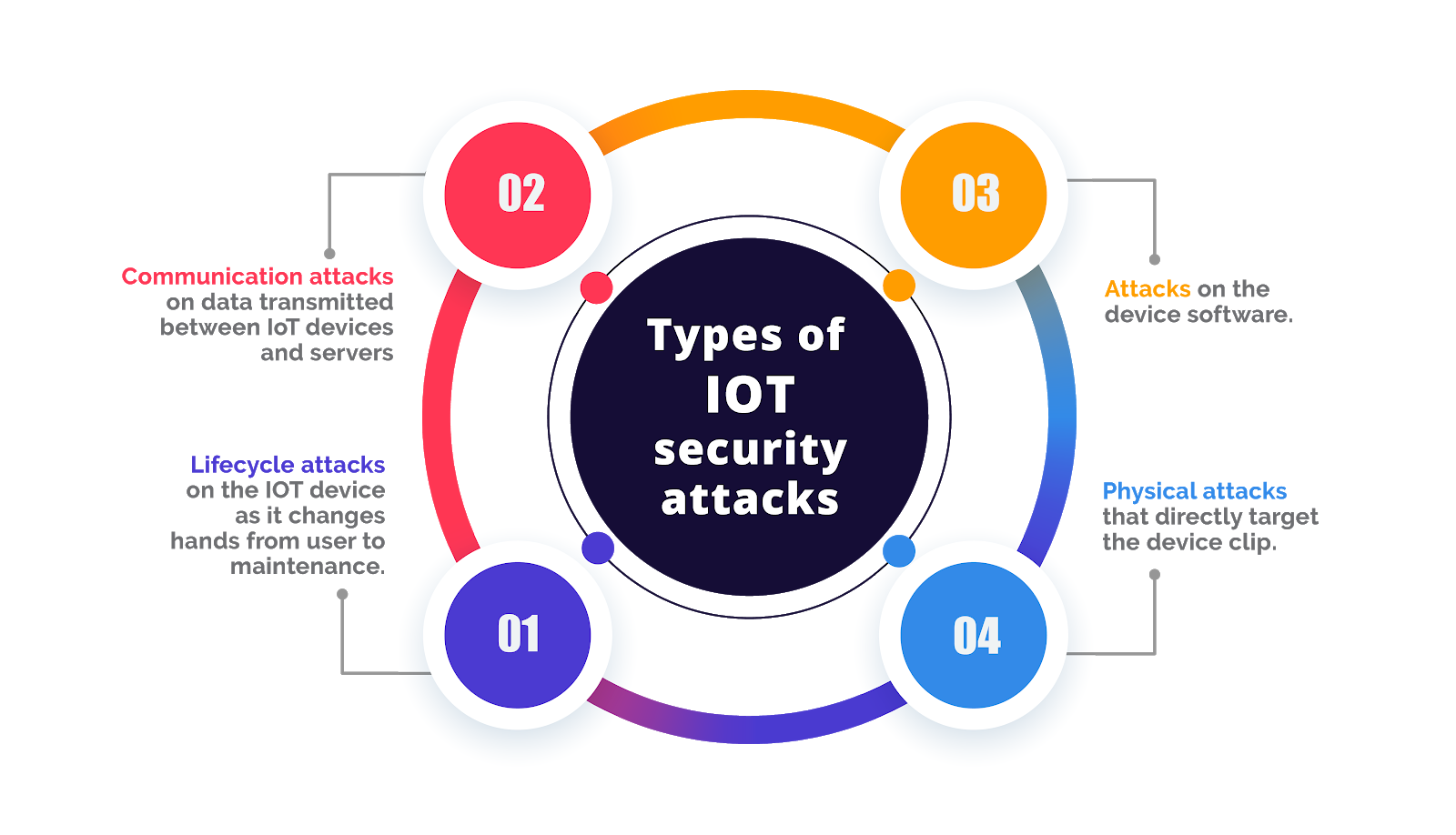
The 5G network infrastructure has brought about new cybersecurity challenges and risks that need to be addressed. The 5G network poses a risk to the security of organizations and individuals alike, as it is more vulnerable to cyber threats than previous networks. The Global Cybersecurity Outlook 2024 revealed significant cyber inequity, exposing stark disparities in resilience between small and large organizations.
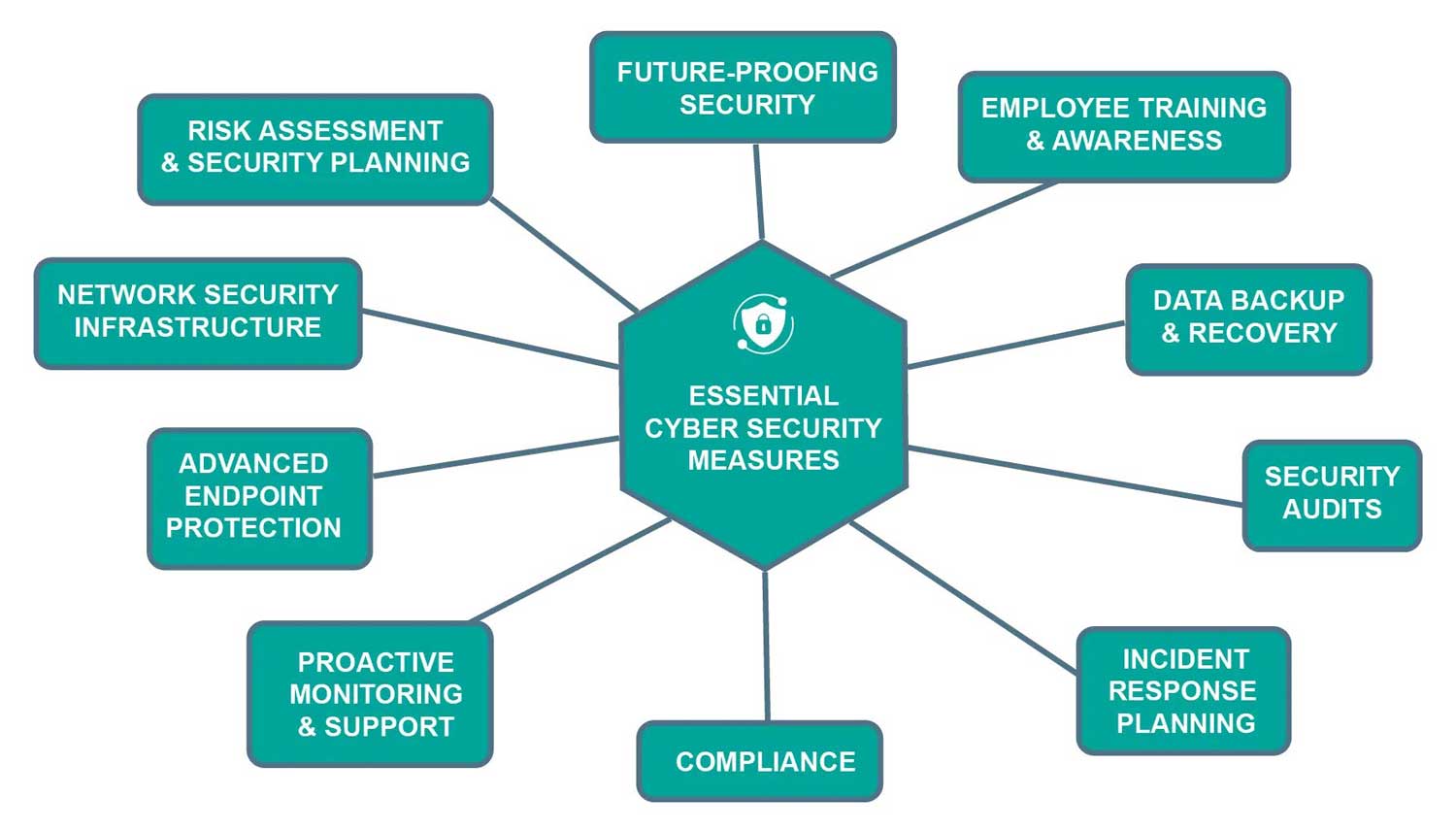
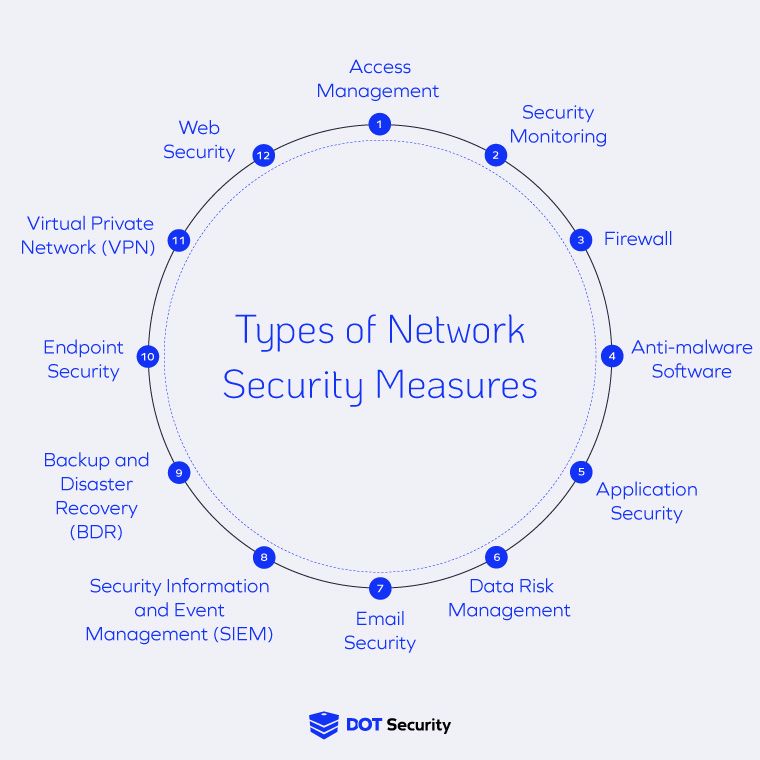
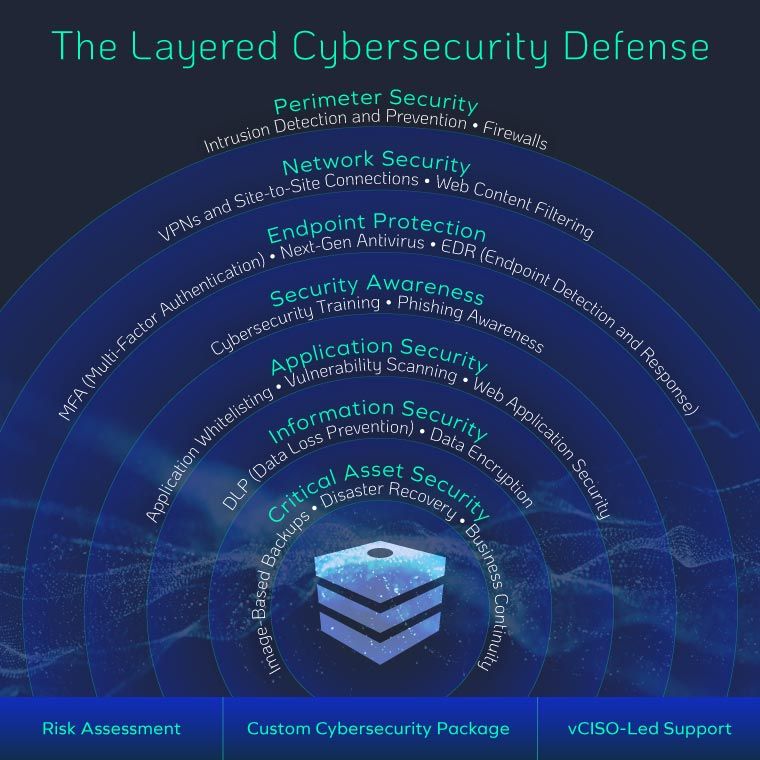
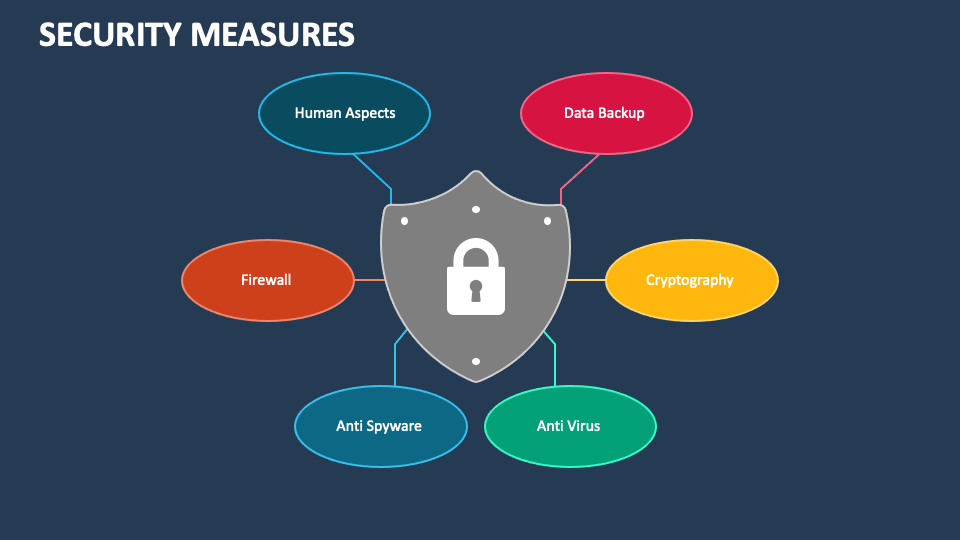
Key Recommendations for Strengthening Wireless Network Security
To strengthen wireless network security, there are several key recommendations that can be followed:
- Implement Strong Authentication and Authorization Mechanisms: This includes using strong passwords, multi-factor authentication, and ensuring that all users and devices are authorized to access the network.
- Use End-to-End Encryption: This will protect data transmitted over the network from interception and eavesdropping.
- Implement Network Segmentation: This will reduce the ability of an adversary to reach and exploit other systems on the network.
- Use Secure Protocols: Use secure communication protocols such as HTTPS and TLS to encrypt data in transit.
- Regularly Update and Patch Vulnerabilities: Regularly update and patch vulnerabilities in the network to prevent exploitation by hackers.

Optimizing Wireless Network for Cybersecurity Measures
Optimizing a wireless network for cybersecurity measures is crucial in preventing cyber threats and ensuring the integrity of the network. By implementing strong authentication and authorization mechanisms, using end-to-end encryption, implementing network segmentation, using secure protocols, and regularly updating and patching vulnerabilities, organizations can significantly reduce the risk of cyber threats.
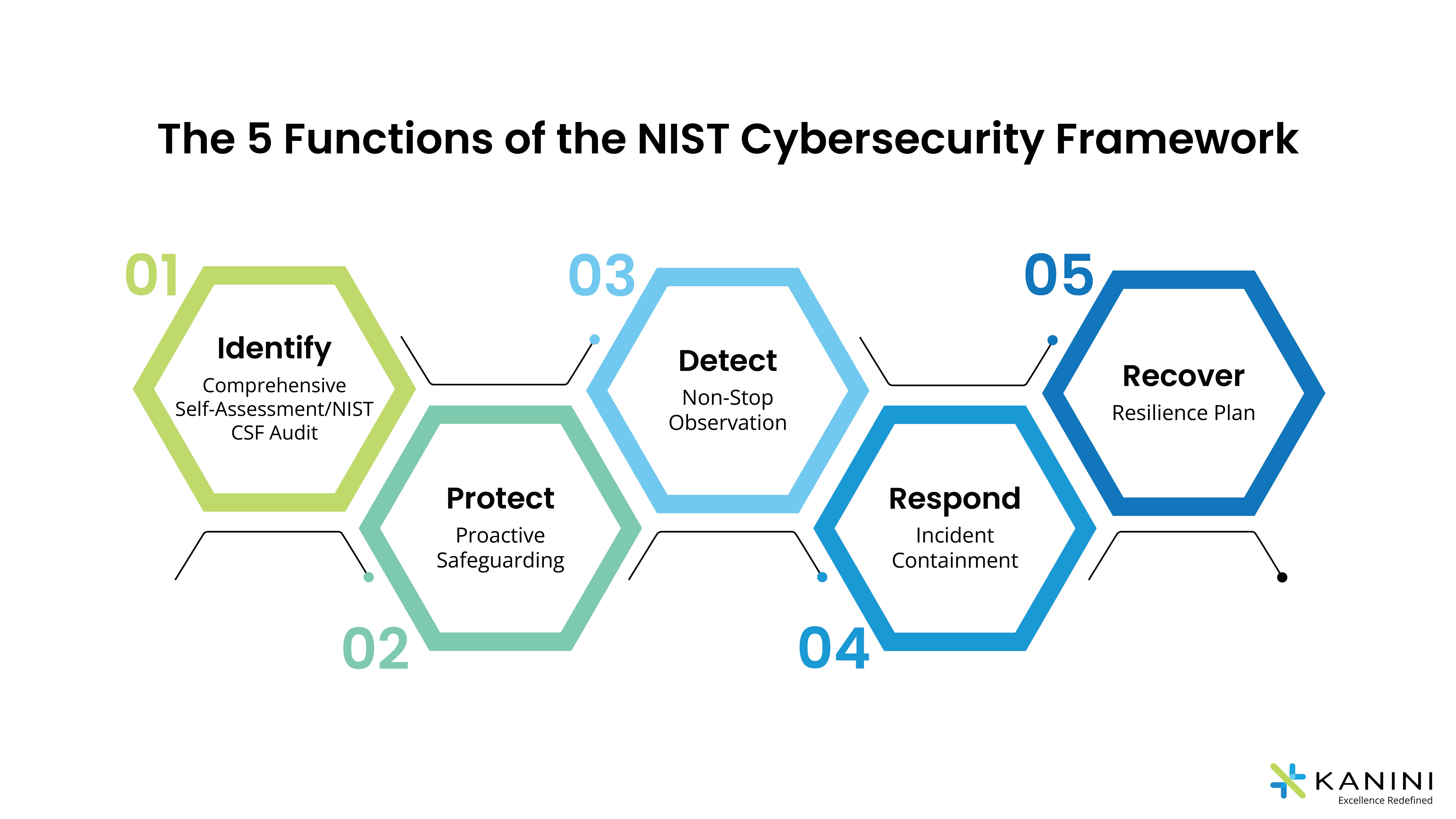
The Importance of Continuous Improvement
Wireless networks are vulnerable to cyber threats, and the evolving sophistication of cyber threats necessitate continuous improvement of security measures. The inherent vulnerabilities of wireless networks coupled with the evolving sophistication of cyber threats necessitate the continuous improvement of security measures to safeguard sensitive information and ensure the integrity of the networks.
Conclusion
In conclusion, optimizing a wireless network for cybersecurity measures is critical in preventing cyber threats and ensuring the integrity of the network. By implementing strong authentication and authorization mechanisms, using end-to-end encryption, implementing network segmentation, using secure protocols, and regularly updating and patching vulnerabilities, organizations can significantly reduce the risk of cyber threats.