G Network Security Setup for Compliance and Governance
Ensuring the security and integrity of a G Network is a top priority for organizations, and a comprehensive Network Security Setup for Compliance and Governance is critical to preventing data breaches and ensuring regulatory compliance. In this article, we will explore the key components of a G Network Security Setup for Compliance and Governance and provide guidance on establishing and enforcing policies, procedures, and standards for managing and protecting your Network and its assets.
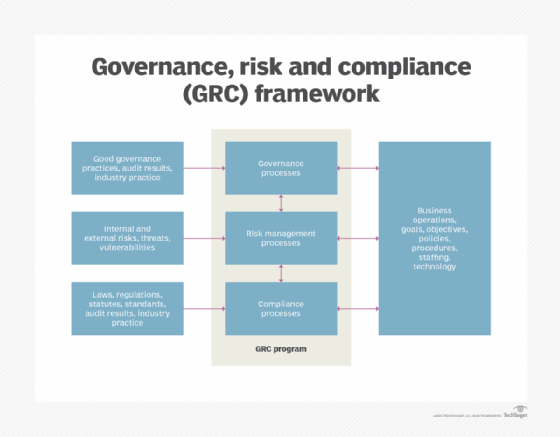
Cybersecurity Governance for Compliance and Governance
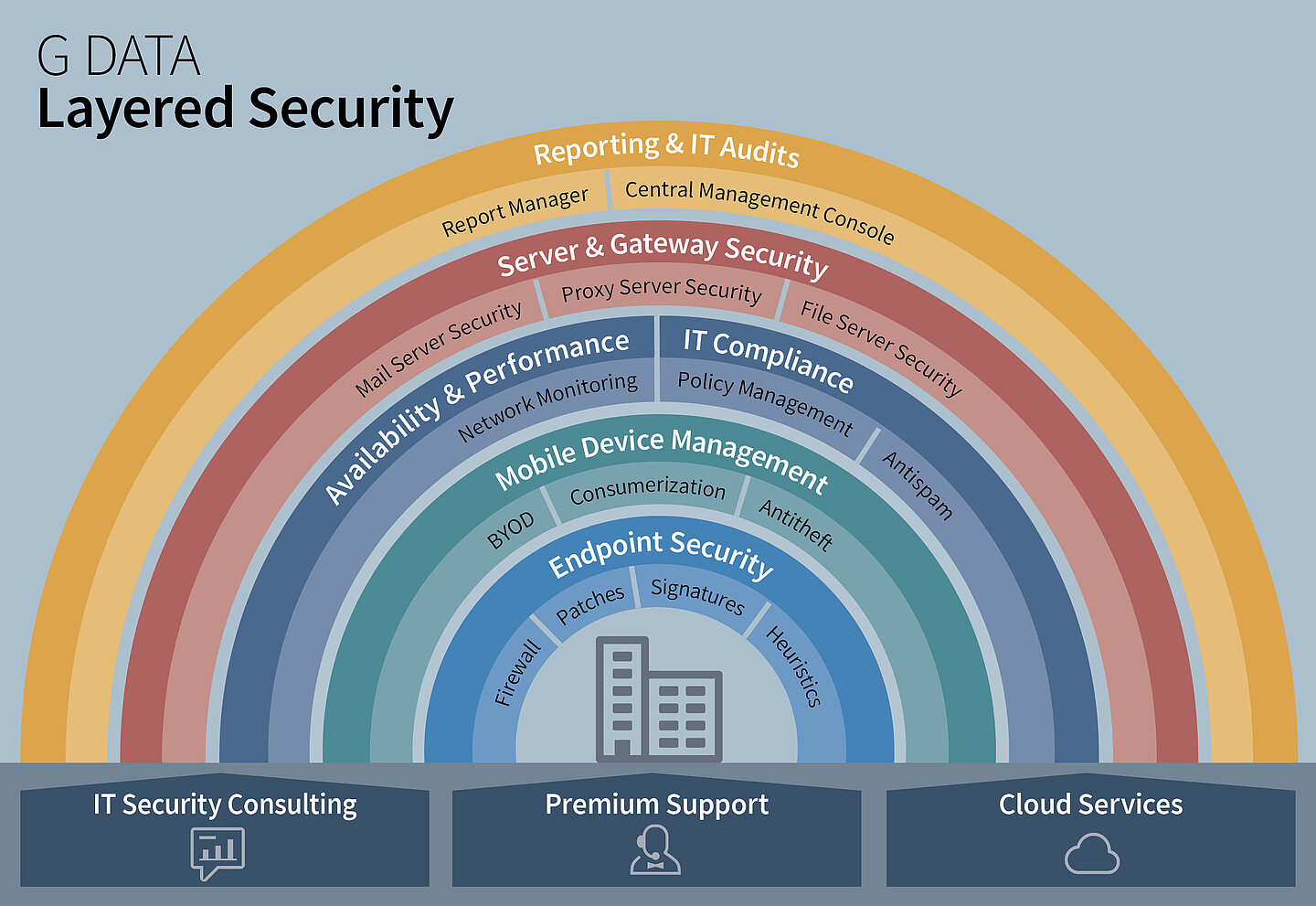
Cybersecurity governance is a comprehensive cybersecurity strategy that integrates with organizational operations and prevents the interruption of activities due to cyber threats or attacks. A cybersecurity governance structure must include strategic alignment, comprehensive policy development, data protection controls, and regular risk management to create a cohesive framework for effective cybersecurity. Leadership engagement is crucial to the success of a cybersecurity governance program, and key elements include:
- Strategic Alignment: Align the cybersecurity governance program with the organization's overall strategic objectives.
- Comprehensive Policy Development: Develop and implement policies and procedures that address cybersecurity and governance.
- Data Protection Controls: Implement data protection controls to ensure the confidentiality, integrity, and availability of sensitive data.
- Regular Risk Management: Conduct regular risk assessments and update the cybersecurity governance program accordingly.
Key Takeaways
Cybersecurity governance integrates a cybersecurity strategy with business goals, fostering risk management and compliance to bolster organizational resilience.
Best Practices for Network Security Setup for Compliance and Governance

Establishing a robust Network Security Setup for Compliance and Governance requires careful consideration of several key elements, including:
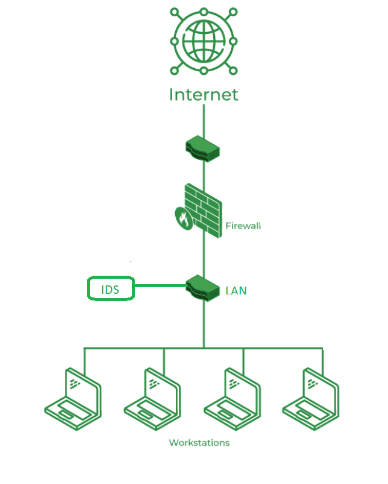
- Network Architecture: Design a network architecture that separates business and non-business networks to prevent unauthorized access.
- Access Control: Implement access controls to ensure that only authorized personnel have access to sensitive data and systems.
- Security Controls: Implement security controls, such as firewalls and intrusion detection systems, to prevent unauthorized access and detect potential security threats.
- Regular Risk Management: Conduct regular risk assessments to identify and mitigate potential security threats.
Regulatory Compliance
Regulatory compliance is a critical aspect of a G Network Security Setup for Compliance and Governance, and organizations must ensure that they are in compliance with relevant regulations and standards. Some key regulations and standards include:
- HIPAA: The Health Insurance Portability and Accountability Act (HIPAA) regulates the handling and storage of sensitive health information.
- GDPR: The General Data Protection Regulation (GDPR) regulates the handling and storage of sensitive personal data within the European Union.
- CCPA: The California Consumer Privacy Act (CCPA) regulates the handling and storage of sensitive personal data within the state of California.
Conclusion
Establishing a robust G Network Security Setup for Compliance and Governance is critical to preventing data breaches and ensuring regulatory compliance. By integrating a cybersecurity strategy with business goals, fostering risk management and compliance, and establishing robust security controls, organizations can ensure the security and integrity of their Network and its assets. In conclusion, a comprehensive Network Security Setup for Compliance and Governance must include several key elements, including strategic alignment, comprehensive policy development, data protection controls, regular risk management, and regulatory compliance.