G Network Security Setup for Data Loss Prevention: A Comprehensive Guide
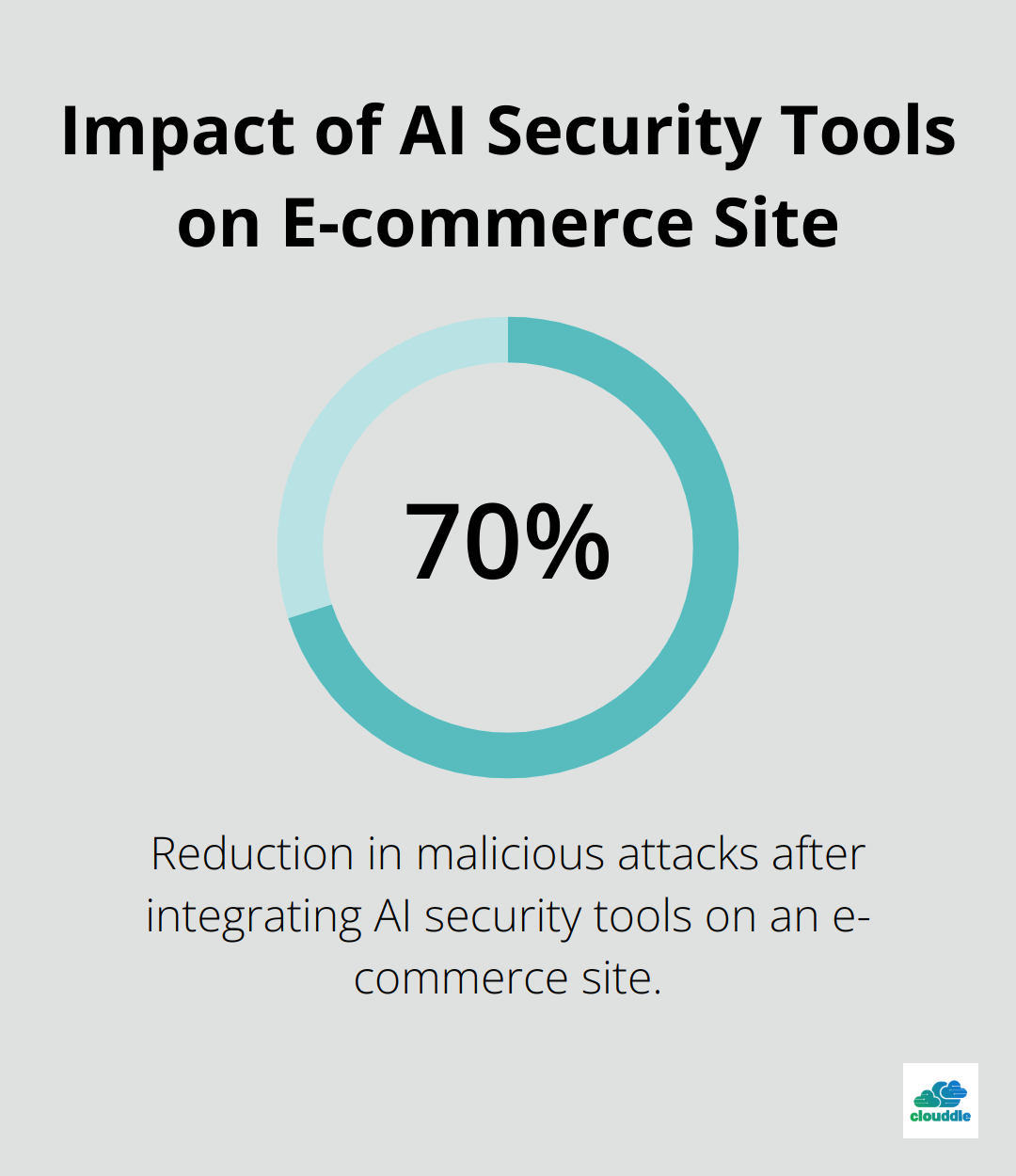
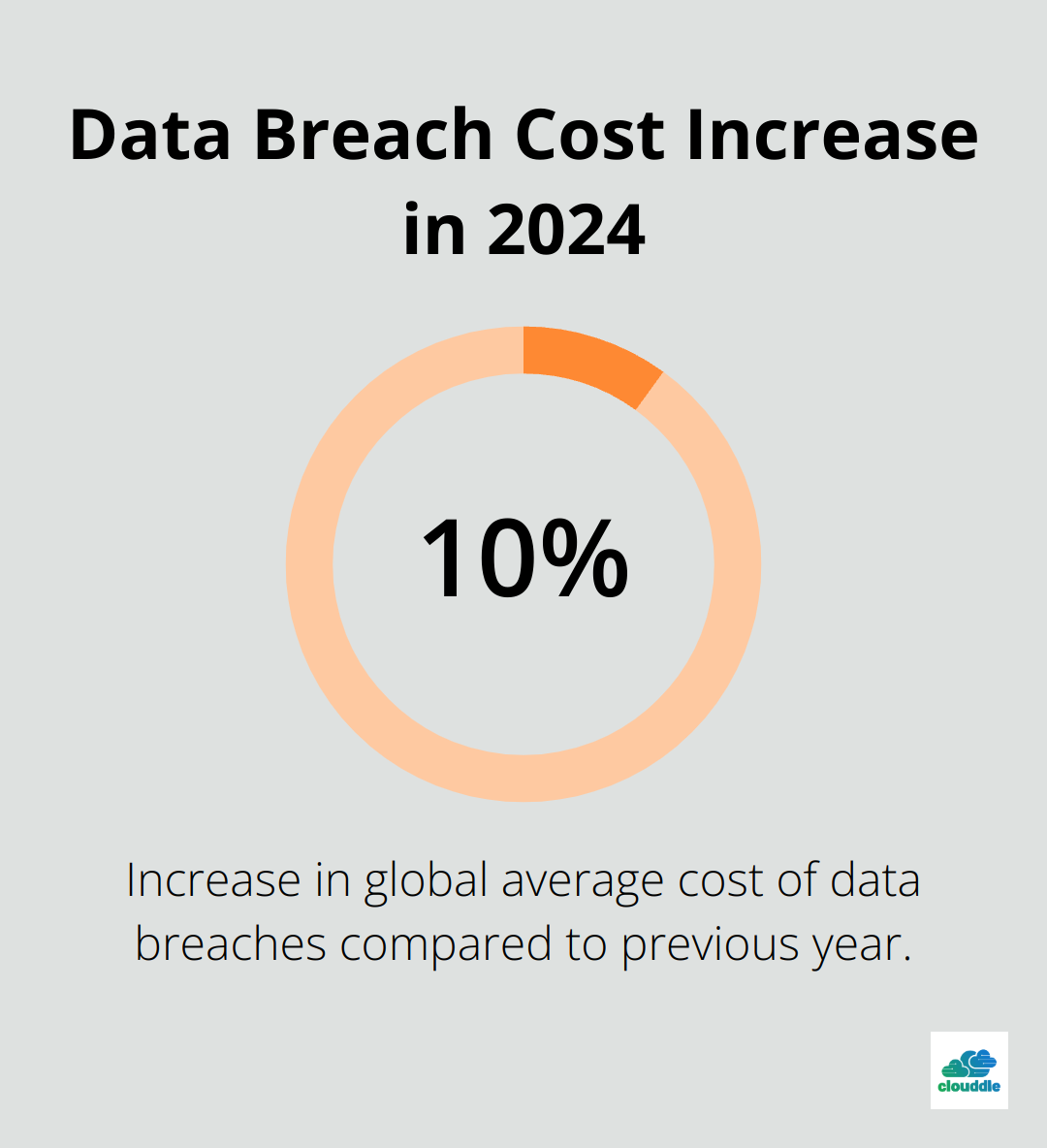
Data loss prevention (DLP) has become a critical aspect of modern network security. With the increasing threat of data breaches and unauthorized data exposure, organizations must implement robust DLP measures to protect sensitive information and ensure regulatory compliance. In this article, we will explore the importance of G Network Security Setup for Data Loss Prevention and provide a step-by-step guide on how to implement a comprehensive DLP strategy.
What is G Network Security Setup for Data Loss Prevention?
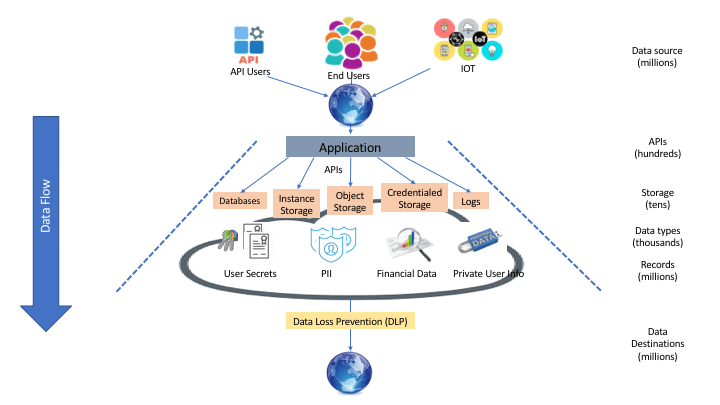
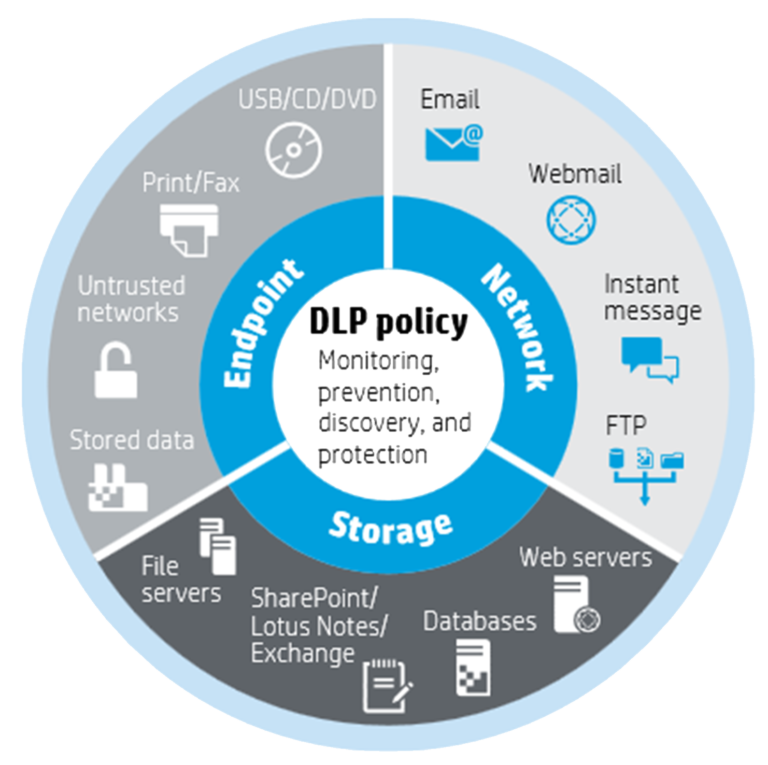
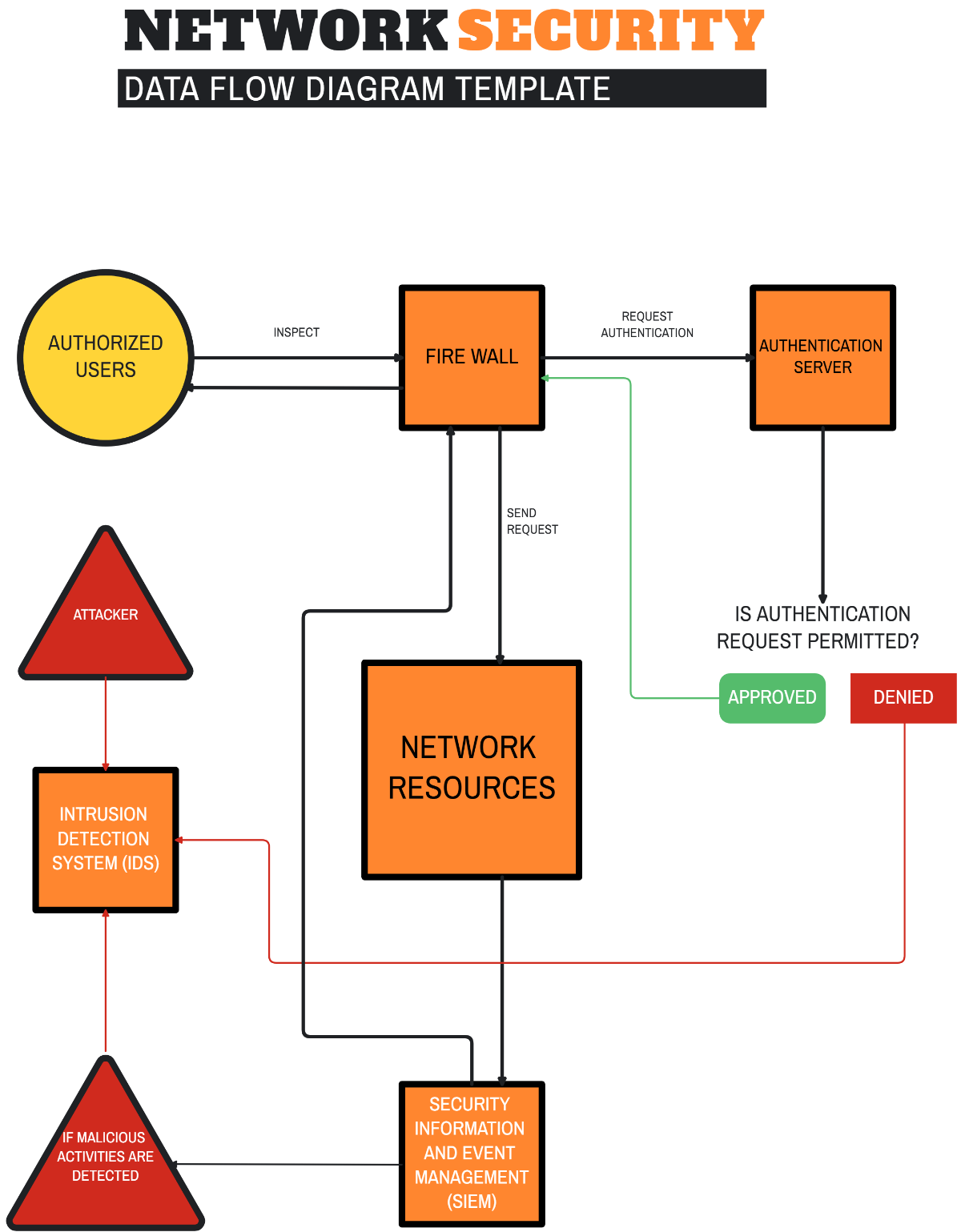
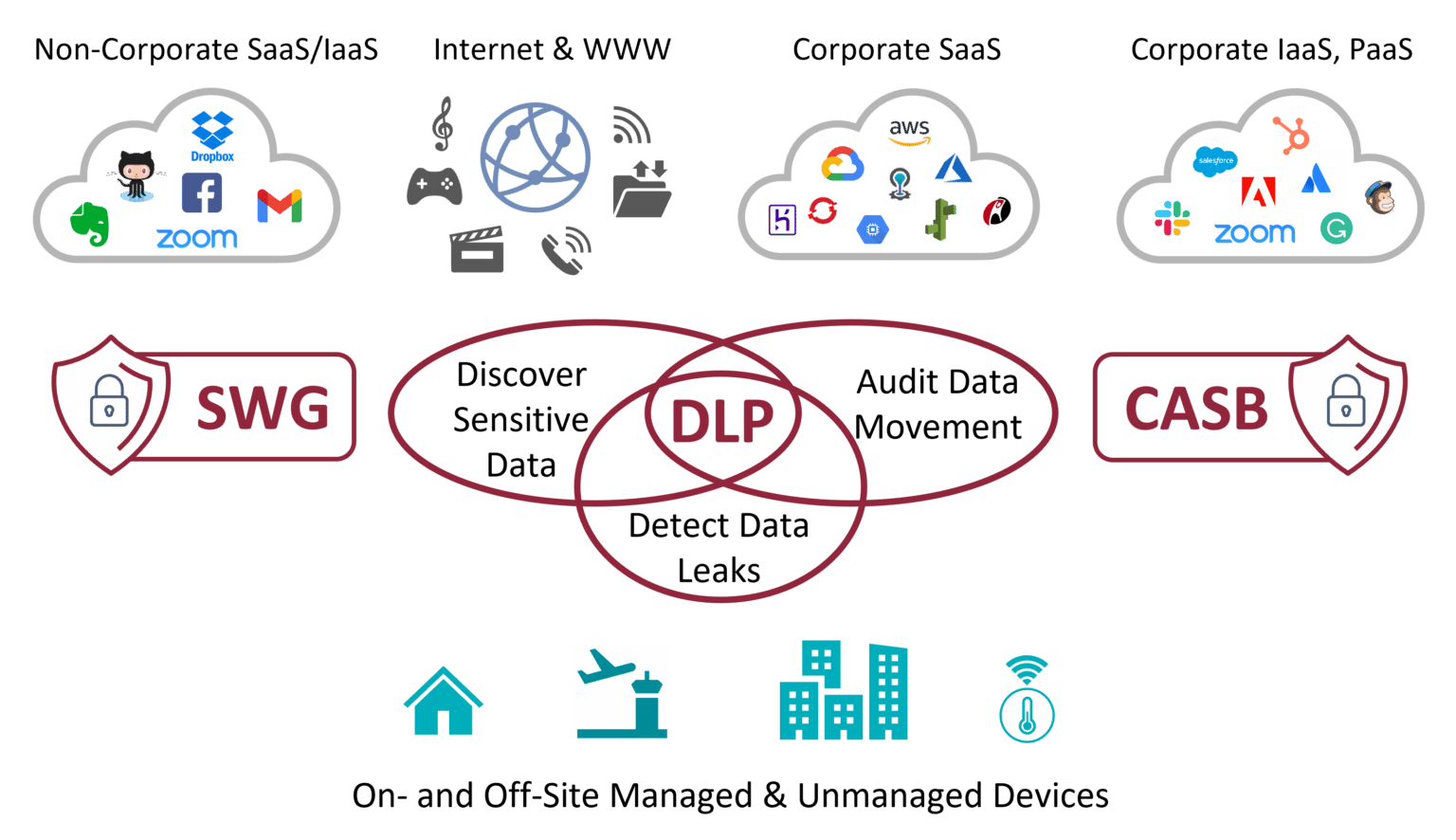
G Network Security Setup for Data Loss Prevention is a network-layer data security solution that uses identity-centric and policy-driven approach to prevent data breaches and unauthorized data exposure. This solution combines Microsoft Purview's data classification service and the identity-centric network security policies in Global Secure Access to create an advanced network-layer data security solution.
Why is G Network Security Setup for Data Loss Prevention Important?
In today's digital landscape, data breaches and unauthorized data exposure have become a significant threat to organizations. A robust DLP strategy is essential to prevent data breaches, protect sensitive information, and ensure regulatory compliance. DLP solutions that identify and prevent the unauthorized sharing, transfer, and use of sensitive data have become essential to addressing data risk in modern businesses.
Types of Data Threats
Data threats can be categorized into three types: insider threats, external threats, and accidental data exposure. Insider threats typically come from employees with authorized access to sensitive data, while external threats come from hackers and other malicious actors. Accidental data exposure occurs when employees unknowingly or unintentionally share sensitive data with unauthorized parties. A comprehensive DLP strategy should address all three types of data threats.
Causes of Data Leaks
Data leaks can occur due to various reasons, including employee negligence, technical failures, or intentional data manipulation. A robust DLP strategy should identify and address the root causes of data leaks to prevent them from happening in the first place. Some common causes of data leaks include:
- Employee negligence
- Technical failures
- Intentional data manipulation
- Phishing attacks
- Malware and ransomware attacks
Prevention Strategies
A comprehensive DLP strategy should involve a combination of technical, administrative, and personnel controls. Some effective DLP prevention strategies include:
- Implementing data classification and labeling
- Using encryption and access controls
- Enforcing data usage policies
- Monitoring and controlling data transfer
- Conducting regular security audits and risk assessments
G Network Security Setup for Data Loss Prevention Steps
Implementing a comprehensive DLP strategy involves several steps. Here are some steps to follow when implementing G Network Security Setup for Data Loss Prevention:
- Assess your data risk: Identify your sensitive data and assess the risk of data breaches.
- Implement data classification and labeling: Classify and label your sensitive data to determine who can access it and under what conditions.
- Use encryption and access controls: Use encryption and access controls to prevent unauthorized access to sensitive data.
- Enforce data usage policies: Enforce data usage policies to ensure employees use sensitive data in compliance with organizational policies.
- Monitor and control data transfer: Monitor and control data transfer to prevent unauthorized data exposure.
- Conduct regular security audits and risk assessments: Conduct regular security audits and risk assessments to identify and address potential security vulnerabilities.
Conclusion
G Network Security Setup for Data Loss Prevention is a comprehensive DLP strategy that combines identity-centric and policy-driven approach to prevent data breaches and unauthorized data exposure. By implementing a robust DLP strategy, organizations can protect sensitive information, prevent data breaches, and ensure regulatory compliance. In this article, we have explored the importance of G Network Security Setup for Data Loss Prevention and provided a step-by-step guide on how to implement a comprehensive DLP strategy. Remember, a robust DLP strategy is essential to addressing data risk in modern businesses.